The following text is a summary of an academic report I wrote together with a friend as part of a course on computer security at Lund University. The paper was graded “A” by the teacher. You can download and read the full report here: Authentication with Passwords & Passphrases – Implications on Usability and Security.pdf
Introduction
A passphrase is a form of password, where several natural language words are used instead of a shorter random sequence of characters. Most password systems can handle passphrases too, making the choice a matter of policy. We sought to explore the implications on usability and security when using passwords and passphrases as an authentication method for information systems. Our objectives were to see how passphrases relate to passwords and how they each affect security and usability, and how security and usability affect each other.
Security
Passwords and passphrases (“secrets”) can be generated by the system or chosen by the user. User selected secrets tend to be less secure secrets and predictable in various ways. A security meter can help users choose a stronger secret. System generated secrets are generally more secure, but have less usability.
Attackers can compromise secrets in many ways. Offline brute force and dictionary attacks can crack even complex secrets today. Online systems are less vulnerable to such attacks, but through social engineering an attacker can compromise these too. There is no conclusive evidence that either passwords or passphrases offer better security than the other. They both have weaknesses that can be exploited, so their security depends on the composition and length, as well as the type of attack. Long secrets using made up words can protect against offline attacks, but not against social engineering, for which user awareness, attitude and education is essential.
Usability
Memory and typographical errors are the errors affecting usability the most when it comes to secrets. Users are more likely to enter passphrases wrong due to their sheer length. This difference tends to disappear as the users get more comfortable using passphrases. There is no evidence that user selected passphrases are easier to remember than user selected passwords. User selected secrets are however easier to remember than system generated secrets. Users also prefer to select their secrets themselves rather than being assigned system generated ones.
 Human Factor
Human Factor
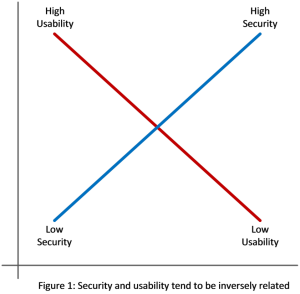
There is an apparent trade-off between usability and strong security, where techniques to increase security tend to decrease the usability and vice versa (figure 1). When the usability is affected negatively by security policies, users may bypass or try to trick the system’s control mechanisms to achieve higher usability. Often users only see authentication as an obstacle that needs to be bypassed to get to the desired information. An example of this can be when users are aware of the security policies but tries to figure out the weakest secret that still complies with the policy when required to changed their password. The secret may comply technically, but the intentions of the policy are lost.
When users bypass security policies they often don’t have a clear understanding of the potential risks they expose the system to. This risk is too abstract for the users to care about, while the authentication barrier they want to overcome is real. Policy makers must thus find a balance that takes into account the security requirements for the systems as well as user satisfaction.
Result
In conclusion, neither passwords nor passphrases offered a big enough benefit to be recommended in front of the other. Many factors affects usability and security. The two tend to be inversely related – improving one impairs the other. Practitioners need to consider both to find a suitable balance for their particular systems. When defining security policies, it is better to design policies that are actually used, rather than something too strict that is circumvented by the users.

